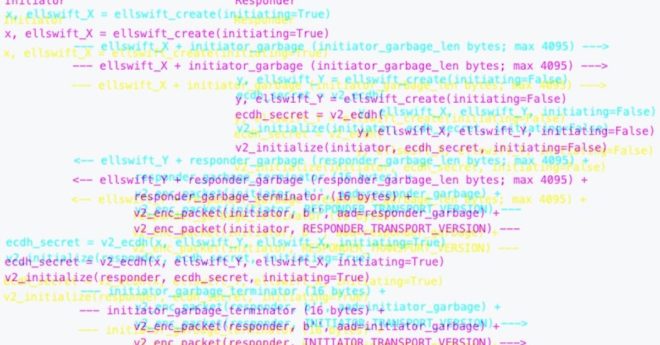
“This proposal for a new P2P protocol version (v2) aims to improve upon this by raising the costs for performing these attacks substantially, primarily through the use of unauthenticated, opportunistic transport encryption,” according to the proposal. A key benefit is that “encryption, even when it is unauthenticated and only used when both endpoints support v2, impedes eavesdropping by forcing the attacker to become active.”
Bitcoin Core’s ‘v26.0’ Upgrade Aims to Impede Eavesdropping, Tampering