The ‘Ledger hacker’ who siphoned away at least $484,000 from multiple Web3 apps on Dec. 14 did so by tricking Web3 users into making malicious token approvals, according to the team behind blockchain security platform Cyvers.
According to public statements made by multiple parties involved, the hack occurred on the morning of Dec. 14. The attacker used a phishing exploit to compromise the computer of a former Ledger employee, gaining access to the employee’s node package manager javascript (NPMJS) account.
We have identified and removed a malicious version of the Ledger Connect Kit.
A genuine version is being pushed to replace the malicious file now. Do not interact with any dApps for the moment. We will keep you informed as the situation evolves.
Your Ledger device and…
— Ledger (@Ledger) December 14, 2023
Once they gained access, they uploaded a malicious update to Ledger Connect’s GitHub repo. Ledger Connect is a commonly used package for Web3 applications.
Some Web3 apps upgraded to the new version, causing their apps to distribute the malicious code to users’ browsers. Web3 apps Zapper, SushiSwap, Phantom, Balancer, and Revoke.cash were infected with the code.
As a result, the attacker was able to siphon away at least $484,000 from users of these apps. Other apps may be affected as well, and experts have warned that the vulnerability may affect the entire Ethereum Virtual Machine (EVM) ecosystem.
How it could have happened
Speaking to Cointelegraph, Cyvers CEO Deddy Lavid, chief technology officer Meir Dolev, and blockchain analyst Hakal Unal shed further light on how the attack may have occurred.
According to them, the attacker likely used malicious code to display confusing transaction data in the user’s wallet, leading the user to approve transactions they didn’t intend to.
When developers create Web3 apps, they use open-source “connect kits” to allow their apps to connect with users’ wallets, Dolev stated. These kits are stock pieces of code that can be installed in multiple apps, allowing them to handle the connection process without needing to spend time writing code. Ledger’s connect kit is one of the options available to handle this task.
It sounds like today’s security incident was the culmination of 3 separate failures at Ledger:
1. Blindly loading code without pinning a specific version and checksum.
2. Not enforcing “2 man rules” around code review and deployment.
3. Not revoking former employee access.— Jameson Lopp (@lopp) December 14, 2023
When a developer first writes their app, they usually install a connect kit through Node Package Manager (NPM). After creating a build and uploading it to their site, their app will contain the connect kit as part of its code, which will then be downloaded into the user’s browser whenever the user visits the site.
According to the Cyvers’ team, the malicious code inserted into the Ledger Connect Kit likely allowed the attacker to alter the transactions being pushed to the user’s wallet. For example, as part of the process of using an app, a user often needs to issue approvals to token contracts, allowing the app to spend tokens out of the user’s wallet.
The malicious code may have caused the user’s wallet to display a token approval confirmation request but with the attacker’s address listed instead of the app’s address. Or, it may have caused a wallet confirmation to appear that would consist of difficult-to-interpret code, causing the user to confusedly push “confirm” without understanding what they were agreeing to.
Blockchain data shows that the victims of the attack made very large token approvals to the malicious contract. For example, the attacker drained over $10,000 from the Ethereum address 0xAE49C1ad3cf1654C1B22a6Ee38dD5Bc4ae08fEF7 in one transaction. The log of this transaction shows that the user approved a very large amount of USDC to be spent by the malicious contract.

This approval was likely performed by the user in error because of the malicious code, said the Cyvers team. They warned that avoiding this kind of attack is extremely difficult, as wallets do not always give users clear information about what they are agreeing to. One security practice that may help is to carefully evaluate each transaction confirmation message that pops up while using an app. However, this may not help if the transaction is displayed in code that is not easily readable or is confusing.
Related: ConsenSys exec on MetaMask Snaps security: ‘Consent is king’
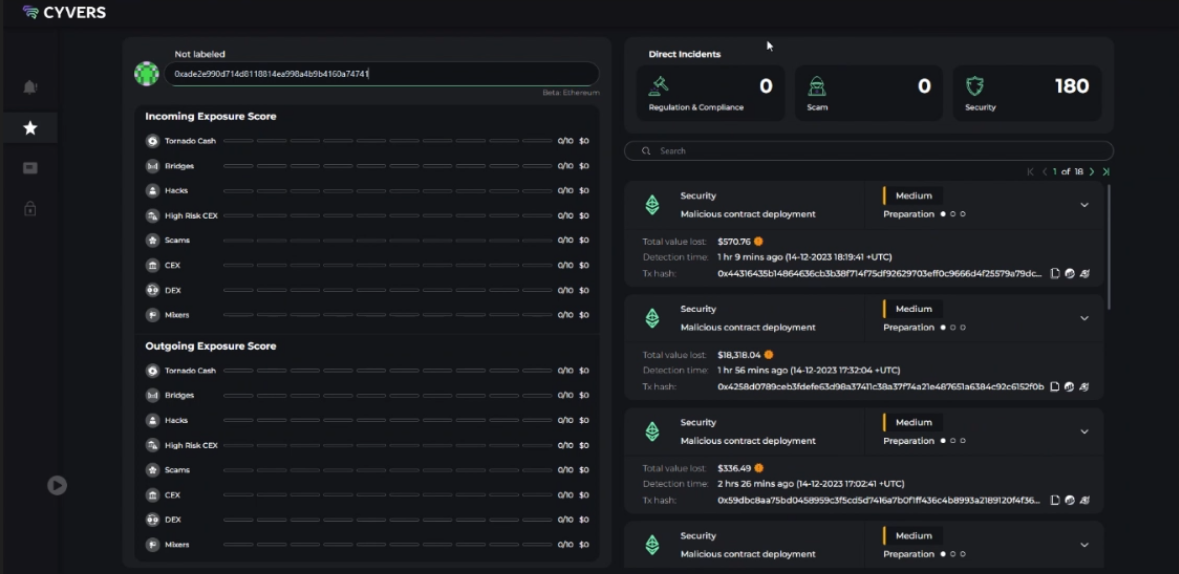
Cyvers claimed that their platform allows businesses to check contract addresses and determine if these addresses have been involved in security incidents. For example, the account that created the smart contracts used in this attack was detected by Cyvers as having been involved in 180 security incidents.
While Web3 tools in the future could allow attacks like these to be detected and thwarted in advance, the industry still has “a long way to go” in solving this problem, the team told Cointelegraph.



